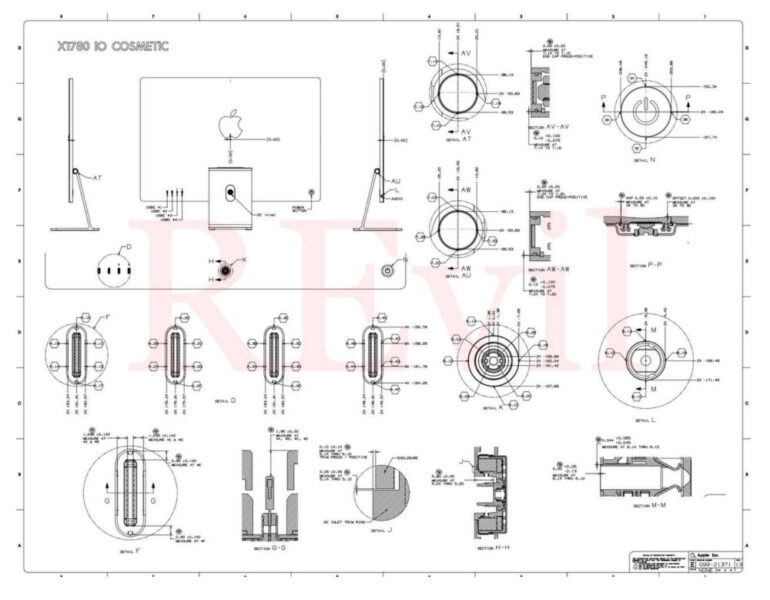
In case you missed it, while Apple held its Spring Loaded event wherein it launched the new iMac, new iPad Pro, and AirTags, Bloomberg reported that a ransomware group called REvil declared that it accessed the internal computers of Apple supplier Quanta Computer Inc. The group managed to obtain 15 images/schematics of unreleased MacBooks from the attack, including “specific component serial numbers, sizes, and capacities detailing the many working parts inside”.
Quanta Computer works with HP, Facebook, and other tech companies but the ransomware group specifically targeted Apple.
A report from Bleeping Computer mentions that the REvil asked Apple to pay an undisclosed ransom for the images/schematics by May 1 in an effort to profit off the stolen data. The group mentions in their blog that they will continue to post new files every day until then.
In a chat with Quanta, REvil revealed it had stolen and encrypted “all local network data” and won’t give it up until the USD 50 million ransom is paid.
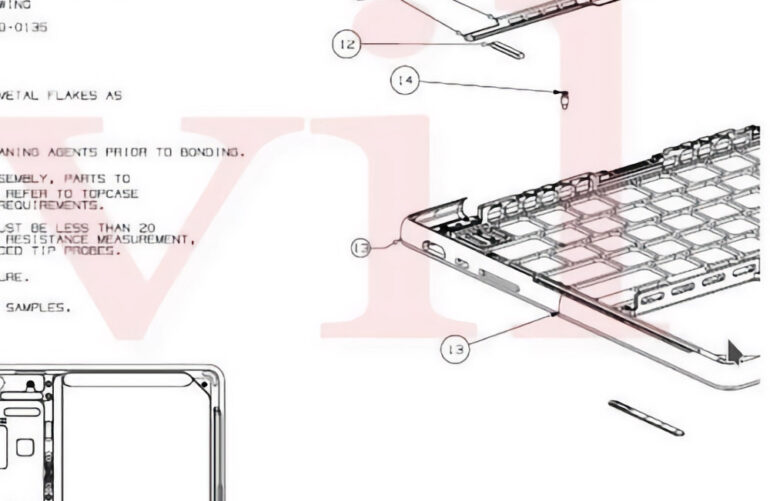
The group has since released documents showcasing the 2021 MacBook Pro logic board, including details and imagery of new ports.

It is detailed that on the right-hand side, the MacBook Pro will have an HDMI port, a USB-C port, and an SD card slot. Meanwhile, on the left side, it will have a MagSafe protector, two USB-C ports, and a headphone jack, according to the documents.
In addition, the 2021 MacBook Pro will also remove the Touch Bar but will retain the Touch ID button on the right side of the function row.

The documents also mention codenames “J314” and “J316” multiple times, which according to Bloomberg, represents the new 14-inch and 16-inch MacBook Pro models.
Apple has yet to comment on the incident and it is uncertain as of writing this, if it will pay for the ransom.
Quanta Computer, on the other hand, acknowledged the attack but didn’t explain how much of its data was stolen.
“Quanta Computer’s information security team has worked with external IT experts in response to cyberattacks on a small number of Quanta servers,” the company said in a statement. “We’ve reported to and kept seamless communications with the relevant law enforcement and data protection authorities concerning recent abnormal activities observed. There’s no material impact on the company’s business operation.”
The supplier is also bolstering its cybersecurity infrastructure following the attack.
Sources 1, 2, 3, 4 | Featured Photo
Ram found his love and appreciation for writing in 2015 having started in the gaming and esports sphere for GG Network. He would then transition to focus more on the world of tech which has also began his journey into learning more about this world. That said though, he still has the mentality of "as long as it works" for his personal gadgets.